Perkoon vs Phishly
Side-by-side comparison to help you choose the right product.
Perkoon enables seamless, free peer-to-peer file transfers without signup, ensuring your files remain private and.
Last updated: March 4, 2026
Phishly
Phishly instantly identifies phishing threats with sophisticated AI for elegant email security.
Visual Comparison
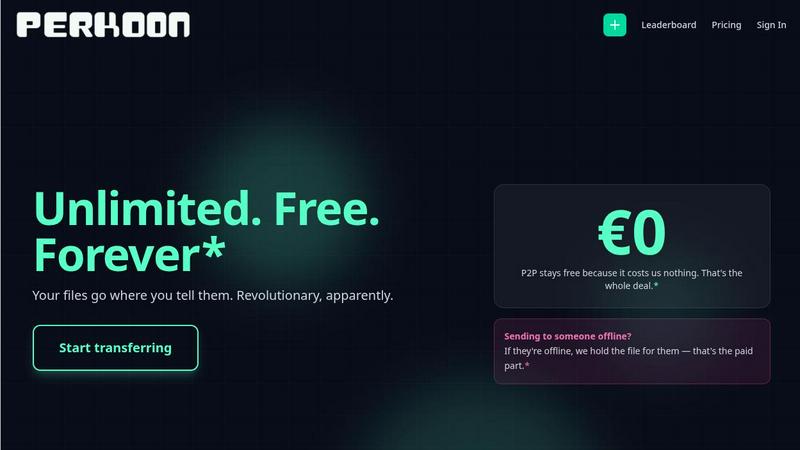
Perkoon
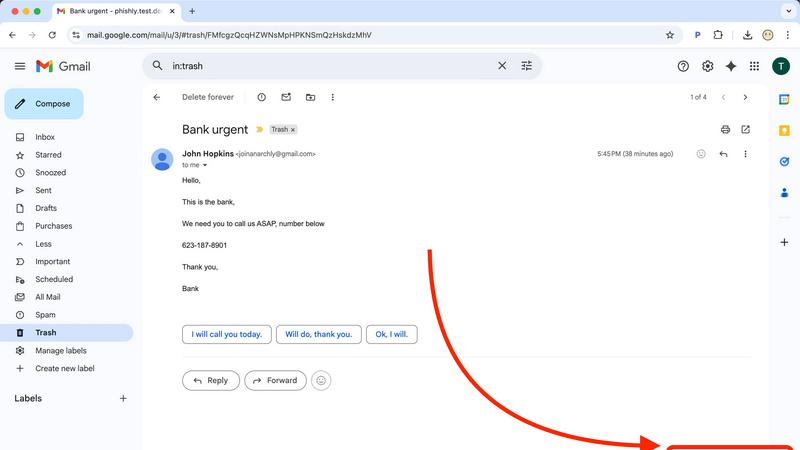
Phishly
Feature Comparison
Perkoon
Peer-to-Peer File Transfers
Perkoon’s flagship feature leverages P2P technology, allowing users to transfer files directly between browsers without the need for a central server. This ensures that transfers are not only instantaneous but also completely private, with no data stored or monitored by Perkoon.
Encrypted Cloud Storage
For situations where the recipient is offline, Perkoon provides an encrypted cloud storage option. This paid feature ensures that files are securely held until the recipient is available to receive them, offering peace of mind about data security and integrity.
AI Integration
Designed for the age of artificial intelligence, Perkoon includes built-in tools that enable AI agents to interact with the service seamlessly. This eliminates the need for outdated screen-scraping techniques, allowing for more efficient and effective file management.
Referral and Rewards Program
Perkoon encourages user growth through its referral program, where users can share unique links to gain additional storage benefits. This community-driven approach not only rewards users but also fosters a collaborative environment where sharing is incentivized.
Phishly
AI-Powered Threat Detection Engine
At the core of Phishly lies a sophisticated artificial intelligence engine trained to identify the nuanced hallmarks of phishing attempts. It goes beyond simple link checking to analyze the complete email context, including domain reputation, header inconsistencies, grammatical anomalies, and the use of urgent or threatening language designed to provoke impulsive action. This multi-layered analysis ensures a high degree of accuracy in distinguishing malicious communications from legitimate ones.
Seamless Gmail Integration via Chrome Extension
Phishly integrates directly into your daily workflow through a discreet yet powerful Chrome extension for Gmail. Once installed, a "Scan with Phishly" button appears within your email client, allowing you to initiate a comprehensive security analysis of any open email without ever leaving your inbox. This frictionless integration means protection is always just one click away, eliminating the need for cumbersome copy-pasting or switching between applications.
Privacy-First, On-Demand Analysis
Upholding a staunch commitment to user privacy, Phishly operates on a strict on-demand model. The system does not scan, read, or analyze any of your emails automatically or without your explicit consent. You maintain complete control, choosing precisely which messages to investigate. This approach ensures your personal and professional correspondence remains confidential, with analysis performed only when you command it.
Clear, Actionable Risk Assessment Reports
Following each scan, Phishly presents its findings not as cryptic technical alerts, but as clear, color-coded risk assessments: Safe, Medium Risk, or High Risk. Each verdict is accompanied by a detailed breakdown explaining the specific factors that contributed to the score, such as a mismatched sender domain, suspicious hyperlinks, or detected social engineering patterns. This transparency educates the user, building digital literacy with every scan.
Use Cases
Perkoon
Quick File Sharing for Teams
Organizations can utilize Perkoon to facilitate rapid file sharing among team members, ensuring that important documents are exchanged in real-time without worrying about file size or transfer limits.
Secure Personal File Transfers
Individuals can depend on Perkoon for sending personal files such as photos or videos to friends and family, confident that their data remains private and secure throughout the transfer process.
Automation for Developers
Developers can leverage Perkoon’s CLI tool within their applications, enabling automated file transfers without the need for complex integration. This enhances productivity and streamlines workflows.
Efficient Data Management for AI Applications
AI professionals can utilize Perkoon’s robust capabilities to transfer datasets efficiently, integrating the service into their workflows to maintain data integrity while simplifying the sharing process.
Phishly
For Vigilant Individual Email Users
Everyday email users who receive a mix of personal and promotional correspondence can use Phishly to instantly verify the legitimacy of unexpected messages. Whether it's a too-good-to-be-true offer, an urgent alert from a supposed bank, or a password reset request, a quick scan provides immediate clarity, preventing costly mistakes and identity theft before any harmful link is clicked or information is shared.
For Small Business Teams and Founders
Small businesses are frequent targets of phishing due to often-limited IT resources. Phishly serves as an invaluable first line of defense for founders and their teams, enabling any employee to safely vet emails claiming to be from vendors, clients, or service providers. This empowers the entire organization to prevent business email compromise (BEC) attacks, fraudulent invoice scams, and credential theft that could lead to significant financial loss.
For Remote Workers and Freelancers
Professionals operating outside traditional corporate security infrastructures can leverage Phishly to secure their independent workflows. When communicating with multiple clients and platforms, the tool helps verify project-related instructions, payment notifications, and file-sharing requests, ensuring that a single deceptive email does not compromise their devices, data, or professional reputation.
For Educational and Non-Profit Organizations
Schools, universities, and non-profits handling sensitive data on constrained budgets find immense value in Phishly's free, easy-to-deploy model. It allows staff and volunteers to safely manage communications regarding donations, event registrations, and administrative matters, fostering a culture of security awareness without the need for expensive, complex enterprise software licenses or dedicated IT staff.
Overview
About Perkoon
Perkoon is an innovative file transfer service that prioritizes simplicity, privacy, and user empowerment. Designed for individuals and organizations disillusioned with conventional file-sharing platforms, Perkoon offers a refreshing alternative by eliminating artificial restrictions and intrusive practices. With its core functionality centered on transferring files seamlessly from point A to point B, Perkoon utilizes cutting-edge peer-to-peer (P2P) technology, allowing users to send files directly between browsers. This means no cumbersome sign-ups, no size limitations, and no data passing through central servers, ensuring both privacy and cost-efficiency. For instances when recipients are offline, Perkoon offers secure cloud storage as a paid feature, thus maintaining transparency about its operational costs. The service stands out with its native design for the AI era, incorporating built-in automation tools and a simple command-line interface (CLI) that allows AI agents to communicate directly with Perkoon. Ultimately, it is a straightforward, powerful, and privacy-centric solution tailored for users who demand more from their file transfer experience.
About Phishly
In the intricate digital landscape where sophisticated phishing campaigns masquerade as legitimate correspondence, Phishly emerges as an essential sentinel for your inbox. This AI-powered platform provides discerning individuals and small to medium-sized enterprises with an elegant, yet formidable, defense against deceptive emails. Available as a seamless Chrome extension for Gmail and a versatile web tool, Phishly empowers users to proactively interrogate any suspicious message with a single click or paste. Its advanced artificial intelligence meticulously scans content for a comprehensive array of phishing indicators—from subtly spoofed sender addresses and dubious domain names to psychologically manipulative language and covert social engineering tactics. The platform then delivers a crystal-clear, actionable risk assessment categorized as Safe, Medium Risk, or High Risk, each accompanied by a detailed, intelligible explanation. Championing a philosophy of absolute privacy and user agency, Phishly only analyzes emails explicitly selected for review, ensuring no unauthorized data access. By distilling complex cybersecurity threat detection into an intuitive, instantaneous, and free-to-use tool, Phishly demystifies digital security, offering peace of mind without the burden of enterprise-level complexity or requiring any technical expertise.
Frequently Asked Questions
Perkoon FAQ
Why is Perkoon free to use?
Perkoon operates on a P2P basis, which incurs minimal operational costs. The service is free because it does not rely on a central server for file transfers, making it sustainable without charging users for this feature.
How does Perkoon keep my data private?
Perkoon’s P2P transfers do not touch any central servers, meaning the files are sent directly between browsers without being stored or scanned. For cloud transfers, files are encrypted to ensure maximum privacy.
What happens if the recipient is offline?
If the intended recipient is offline, Perkoon uses its encrypted cloud storage to hold the files securely until the recipient is ready to receive them. This feature is part of the paid service, ensuring data remains safe during the transfer.
Which browsers are compatible with Perkoon?
Perkoon supports a range of popular browsers, including Chrome, Edge, and Brave, which allow for seamless file transfers. Users of Firefox and Safari should note that there may be some restrictions due to browser limitations.
Phishly FAQ
How does Phishly protect my privacy?
Phishly is built on a foundational principle of user privacy and consent. Our tool does not automatically scan, access, or read any of your emails. Analysis occurs only when you explicitly initiate it by clicking the "Scan with Phishly" button in Gmail or pasting email text into our web tool. We analyze only the content you submit for that specific scan and do not store personal email data or correspondence.
What kinds of phishing indicators does the AI detect?
Our advanced AI model is trained to detect a wide spectrum of phishing indicators. This includes technical red flags like suspicious sender domains, IP mismatches, and poorly crafted email headers. It also analyzes content for psychological triggers such as urgent or threatening language, spoofed brand logos, requests for sensitive information, and subtle social engineering tactics designed to manipulate the recipient into taking a risky action.
Is technical knowledge required to use Phishly?
Absolutely not. Phishly is designed for simplicity and immediacy. The Chrome extension integrates seamlessly into Gmail with a single, clear button. The web tool requires only that you paste text. The results are presented in plain language with straightforward risk ratings (Safe, Medium Risk, High Risk) and explanatory details, making sophisticated threat intelligence accessible to everyone, regardless of technical background.
What is the cost to use Phishly?
Phishly is currently free to use. Our mission is to make essential phishing detection accessible to individuals, small businesses, and organizations that need it most. You can install the Chrome extension and use the web analysis tool without any subscription fees or usage limits, delivering instant, reliable security insights at no cost.