Phishly vs RocketShare
Side-by-side comparison to help you choose the right product.
Phishly
Phishly instantly identifies phishing threats with sophisticated AI for elegant email security.
RocketShare
RocketShare ensures your private files remain exclusively yours with client-side encryption.
Last updated: March 4, 2026
Visual Comparison
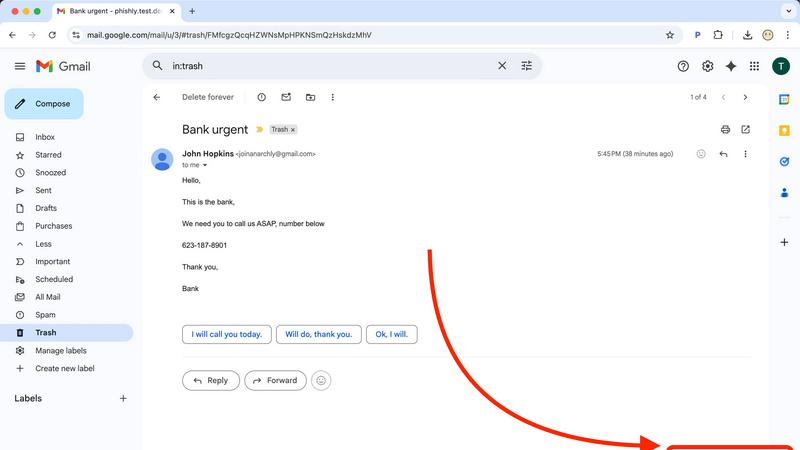
Phishly
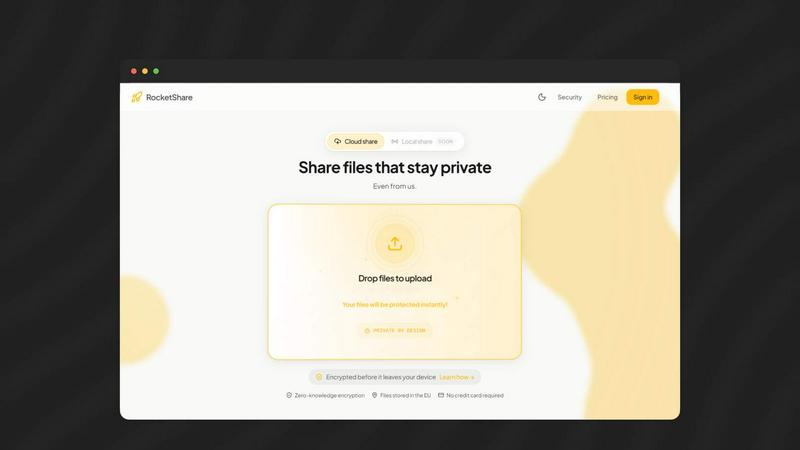
RocketShare
Feature Comparison
Phishly
AI-Powered Threat Detection Engine
At the core of Phishly lies a sophisticated artificial intelligence engine trained to identify the nuanced hallmarks of phishing attempts. It goes beyond simple link checking to analyze the complete email context, including domain reputation, header inconsistencies, grammatical anomalies, and the use of urgent or threatening language designed to provoke impulsive action. This multi-layered analysis ensures a high degree of accuracy in distinguishing malicious communications from legitimate ones.
Seamless Gmail Integration via Chrome Extension
Phishly integrates directly into your daily workflow through a discreet yet powerful Chrome extension for Gmail. Once installed, a "Scan with Phishly" button appears within your email client, allowing you to initiate a comprehensive security analysis of any open email without ever leaving your inbox. This frictionless integration means protection is always just one click away, eliminating the need for cumbersome copy-pasting or switching between applications.
Privacy-First, On-Demand Analysis
Upholding a staunch commitment to user privacy, Phishly operates on a strict on-demand model. The system does not scan, read, or analyze any of your emails automatically or without your explicit consent. You maintain complete control, choosing precisely which messages to investigate. This approach ensures your personal and professional correspondence remains confidential, with analysis performed only when you command it.
Clear, Actionable Risk Assessment Reports
Following each scan, Phishly presents its findings not as cryptic technical alerts, but as clear, color-coded risk assessments: Safe, Medium Risk, or High Risk. Each verdict is accompanied by a detailed breakdown explaining the specific factors that contributed to the score, such as a mismatched sender domain, suspicious hyperlinks, or detected social engineering patterns. This transparency educates the user, building digital literacy with every scan.
RocketShare
Zero-Knowledge End-to-End Encryption
This foundational feature ensures absolute privacy by encrypting your files on your own device before they are uploaded. The encryption key is never transmitted to or stored on RocketShare's servers; it remains solely with you, often embedded within the shareable link itself. Consequently, the platform operates with "zero knowledge" of your file contents, providing a security guarantee that not even a data breach at the server level could expose your sensitive information.
Dual Sharing Modes: Cloud and Local
RocketShare offers versatile transfer methods to suit different security and speed requirements. The Cloud Share option provides convenient, encrypted storage in secure, EU-based data centers for asynchronous access. The Local Share (peer-to-peer) mode enables direct device-to-device transfers over the internet, with files never residing on a central server, ideal for highly sensitive data or when maximum transfer speed is desired.
EU-Based Data Sovereignty
All files shared via the cloud are stored exclusively within data centers located in the European Union. This ensures adherence to some of the world's most stringent data protection regulations, such as the GDPR, providing users with legal certainty and robust privacy safeguards regarding the geographic location and jurisdiction governing their stored data.
Simple, Self-Serve Interface
Despite its powerful security underpinnings, RocketShare is designed for immediate usability. The platform features an intuitive, drag-and-drop interface that requires no technical expertise or complex configuration. This elegant design philosophy ensures that top-tier security is accessible to every user, from individual freelancers to large enterprise teams, without the need for extensive training or IT support.
Use Cases
Phishly
For Vigilant Individual Email Users
Everyday email users who receive a mix of personal and promotional correspondence can use Phishly to instantly verify the legitimacy of unexpected messages. Whether it's a too-good-to-be-true offer, an urgent alert from a supposed bank, or a password reset request, a quick scan provides immediate clarity, preventing costly mistakes and identity theft before any harmful link is clicked or information is shared.
For Small Business Teams and Founders
Small businesses are frequent targets of phishing due to often-limited IT resources. Phishly serves as an invaluable first line of defense for founders and their teams, enabling any employee to safely vet emails claiming to be from vendors, clients, or service providers. This empowers the entire organization to prevent business email compromise (BEC) attacks, fraudulent invoice scams, and credential theft that could lead to significant financial loss.
For Remote Workers and Freelancers
Professionals operating outside traditional corporate security infrastructures can leverage Phishly to secure their independent workflows. When communicating with multiple clients and platforms, the tool helps verify project-related instructions, payment notifications, and file-sharing requests, ensuring that a single deceptive email does not compromise their devices, data, or professional reputation.
For Educational and Non-Profit Organizations
Schools, universities, and non-profits handling sensitive data on constrained budgets find immense value in Phishly's free, easy-to-deploy model. It allows staff and volunteers to safely manage communications regarding donations, event registrations, and administrative matters, fostering a culture of security awareness without the need for expensive, complex enterprise software licenses or dedicated IT staff.
RocketShare
Legal Document Exchange
Law firms and legal professionals routinely handle highly confidential case files, contracts, and evidence. RocketShare enables the secure transmission of these sensitive documents to clients, co-counsel, and experts, with the ironclad guarantee that attorney-client privilege and data integrity are maintained through zero-knowledge encryption, mitigating risk in every exchange.
Creative Asset Delivery
Photographers, videographers, and design agencies can deliver high-resolution client galleries, video edits, and campaign assets with confidence. RocketShare protects their intellectual property from unauthorized access or interception, ensuring that creative work is shared privately and professionally, while also providing a secure channel for client feedback on unpublished projects.
Healthcare Information Handling
Medical practices, therapists, and research institutions can share patient records, diagnostic images, and confidential reports in compliance with strict privacy regulations like HIPAA. The platform's encryption-first model and EU data storage provide a secure framework for communicating sensitive health information between professionals and affiliated organizations.
Confidential Corporate Collaboration
Teams working on strategic plans, financial forecasts, merger documents, or proprietary R&D need a secure collaboration channel. RocketShare facilitates the safe sharing of confidential project files among internal teams and external partners, ensuring that competitive intelligence and trade secrets remain protected throughout the development lifecycle.
Overview
About Phishly
In the intricate digital landscape where sophisticated phishing campaigns masquerade as legitimate correspondence, Phishly emerges as an essential sentinel for your inbox. This AI-powered platform provides discerning individuals and small to medium-sized enterprises with an elegant, yet formidable, defense against deceptive emails. Available as a seamless Chrome extension for Gmail and a versatile web tool, Phishly empowers users to proactively interrogate any suspicious message with a single click or paste. Its advanced artificial intelligence meticulously scans content for a comprehensive array of phishing indicators—from subtly spoofed sender addresses and dubious domain names to psychologically manipulative language and covert social engineering tactics. The platform then delivers a crystal-clear, actionable risk assessment categorized as Safe, Medium Risk, or High Risk, each accompanied by a detailed, intelligible explanation. Championing a philosophy of absolute privacy and user agency, Phishly only analyzes emails explicitly selected for review, ensuring no unauthorized data access. By distilling complex cybersecurity threat detection into an intuitive, instantaneous, and free-to-use tool, Phishly demystifies digital security, offering peace of mind without the burden of enterprise-level complexity or requiring any technical expertise.
About RocketShare
RocketShare is the definitive solution for secure digital collaboration, engineered for those for whom privacy is paramount. It transcends conventional file-sharing by implementing a zero-knowledge encryption architecture, ensuring that your data remains exclusively yours. Every document, image, and file is encrypted directly on your device before transmission, rendering it unreadable to anyone without the unique key—including RocketShare itself. This model provides enterprise-grade security through an elegantly simple interface, eliminating complexity without compromising on protection. Tailored for professionals across legal, creative, healthcare, and corporate sectors, RocketShare facilitates the seamless exchange of files of any size with absolute confidence. With dual sharing modes—secure cloud storage in EU-based data centers and direct local peer-to-peer transfers—it offers unparalleled flexibility. RocketShare is more than a tool; it is a commitment to the principle that true simplicity is found in uncompromising security, safeguarding your intellectual property and confidential communications in an increasingly transparent digital world.
Frequently Asked Questions
Phishly FAQ
How does Phishly protect my privacy?
Phishly is built on a foundational principle of user privacy and consent. Our tool does not automatically scan, access, or read any of your emails. Analysis occurs only when you explicitly initiate it by clicking the "Scan with Phishly" button in Gmail or pasting email text into our web tool. We analyze only the content you submit for that specific scan and do not store personal email data or correspondence.
What kinds of phishing indicators does the AI detect?
Our advanced AI model is trained to detect a wide spectrum of phishing indicators. This includes technical red flags like suspicious sender domains, IP mismatches, and poorly crafted email headers. It also analyzes content for psychological triggers such as urgent or threatening language, spoofed brand logos, requests for sensitive information, and subtle social engineering tactics designed to manipulate the recipient into taking a risky action.
Is technical knowledge required to use Phishly?
Absolutely not. Phishly is designed for simplicity and immediacy. The Chrome extension integrates seamlessly into Gmail with a single, clear button. The web tool requires only that you paste text. The results are presented in plain language with straightforward risk ratings (Safe, Medium Risk, High Risk) and explanatory details, making sophisticated threat intelligence accessible to everyone, regardless of technical background.
What is the cost to use Phishly?
Phishly is currently free to use. Our mission is to make essential phishing detection accessible to individuals, small businesses, and organizations that need it most. You can install the Chrome extension and use the web analysis tool without any subscription fees or usage limits, delivering instant, reliable security insights at no cost.
RocketShare FAQ
How does zero-knowledge encryption work with RocketShare?
Zero-knowledge encryption means your files are encrypted on your device using a unique key before they leave for our servers. Only you possess this decryption key, which is often part of the share link. We never have access to the key or the unencrypted data. Our servers only store and handle the encrypted, unreadable data, making it impossible for us or any third party to access your file contents.
What is the difference between Cloud Share and Local Share?
Cloud Share uploads your encrypted file to our secure, EU-based servers, generating a link you can share. The recipient downloads the file from our servers. Local Share establishes a direct, encrypted peer-to-peer connection between your device and the recipient's device over the internet; the file is transferred directly and never stored on our servers, offering an additional layer of privacy and often faster speeds.
Where are my files stored?
For files shared via Cloud Share, all encrypted data is stored exclusively on our secure servers located within data centers in the European Union. This ensures compliance with robust EU data protection laws. For Local Share transfers, files are never stored on our servers; they travel directly between the devices involved in the transfer.
Is a credit card required to start using RocketShare?
No, you can begin using RocketShare's core secure sharing features immediately without providing a credit card. We believe in offering transparent, accessible security, allowing you to experience the full value of our privacy-by-design platform before any commitment.