Fusedash vs Threat Watch
Side-by-side comparison to help you choose the right product.
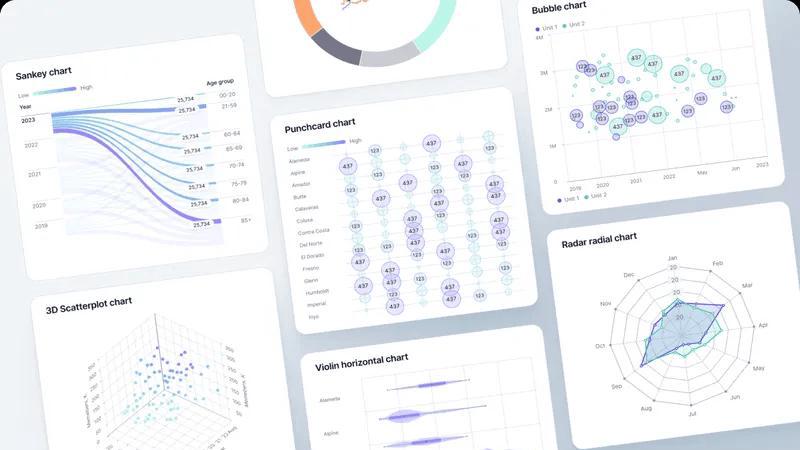
Fusedash transforms raw data into elegant, actionable dashboards and charts for instant team insights.
Last updated: March 4, 2026
Threat Watch
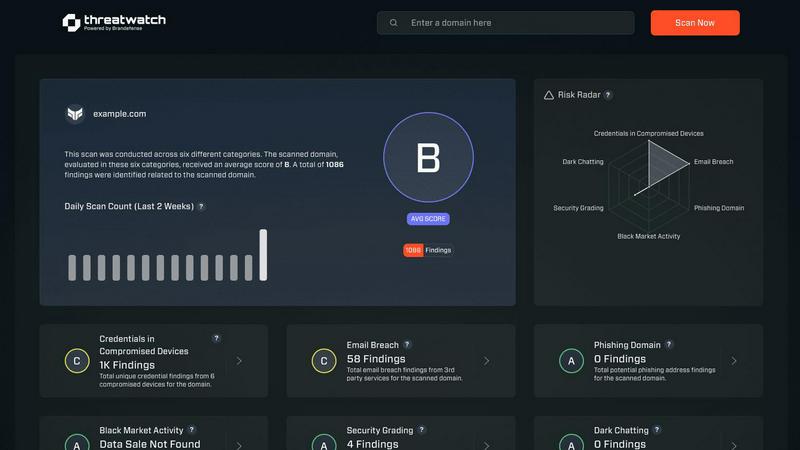
Threat Watch swiftly assesses your cybersecurity health, revealing vulnerabilities in compromised devices and accounts.
Last updated: March 1, 2026
Visual Comparison
Fusedash
Threat Watch
Feature Comparison
Fusedash
Unified AI Visualization Workspace
Fusedash consolidates the entire data visualization lifecycle into one elegant environment. Move fluidly between creating interactive dashboards for real-time KPI monitoring, generating standalone AI-powered charts, crafting detailed geographic maps, and authoring contextual narrative reports. This eliminates the need to rebuild logic across disconnected tools, ensuring every visual and insight originates from the same consistent dataset and metric definitions, saving invaluable time and eradicating reporting discrepancies.
AI Chart Generator
Accelerate insight discovery with an intelligent chart generator that transforms your CSVs or API data into clear, compelling visuals in minutes. This feature intelligently suggests optimal chart types, applies meaningful comparisons, and helps refine labels to ensure each visual accurately tells your data's story. Generated charts can serve as powerful standalone assets or be seamlessly integrated into broader dashboards and reports, providing a fast track from raw data to understood insight.
Contextual Storytelling & Reporting
Bridge the gap between data presentation and strategic understanding with integrated storytelling. Fusedash allows you to combine performance dashboards with narrative context, explaining what changed, why it matters, and what the next steps should be. This transforms static reports into dynamic, communicative documents that provide stakeholders with not just the numbers, but the crucial context needed for alignment and confident decision-making.
Smart Data Chat & Exploration
Navigate your data with conversational ease using Fusedash's integrated AI chat. Pose questions in plain language to explore breakdowns, uncover trends, and receive intelligent suggestions for relevant metrics or visualizations. This natural interface democratizes data exploration, allowing users of all technical skill levels to interrogate information and instantly transform their discoveries into shareable, persistent dashboard views.
Threat Watch
Continuous Threat Monitoring
Threat Watch provides real-time monitoring of your digital assets, ensuring that you are always aware of potential threats and vulnerabilities. This continuous vigilance enables organizations to respond swiftly to emerging risks and enhance their overall security posture.
Dark Web Surveillance
With a dedicated focus on the dark web, Threat Watch continuously scans for compromised credentials, breached accounts, and phishing addresses. This proactive surveillance allows organizations to detect threats before they can be exploited, significantly reducing the risk of data breaches.
Comprehensive Vulnerability Assessment
The platform evaluates critical security categories, delivering a detailed analysis of your organization's vulnerabilities. This feature empowers IT managers and security leaders to prioritize remediation efforts based on the most pressing risks identified within their systems.
Intuitive Dashboard and Reporting
Threat Watch features an elegant, user-friendly dashboard that synthesizes vast amounts of threat intelligence into actionable insights. The intuitive interface allows users to quickly identify critical risks and generate reports that facilitate informed decision-making and strategic planning.
Use Cases
Fusedash
Executive Leadership & Board Reporting
Provide leadership with a consistent, high-level view of organizational health. Fusedash enables the creation of executive dashboards that aggregate key financial, operational, and customer metrics, complemented by narrative storytelling that highlights achievements, explains variances, and outlines strategic forecasts, ensuring all decision-makers are informed by a single, reliable source of truth.
Marketing Performance & Campaign Analysis
Empower marketing teams to move beyond spreadsheets. Connect advertising platform APIs, CRM data, and web analytics to build dynamic dashboards that track campaign ROI, channel performance, and lead generation in real-time. Use segmentation and drill-downs to understand audience behavior and optimize spend, while sharing clear, visual reports with stakeholders to demonstrate impact.
Operational Monitoring & Geographic Insight
Monitor real-time operational metrics across locations or regions. By integrating map-based visualizations, teams in logistics, retail, or field services can instantly see performance geographically, identify hotspots or underperforming areas, and drill down to understand local drivers. This provides an intuitive, at-a-glance understanding of distributed operations.
Cross-Departmental KPI Alignment
Eliminate departmental silos and conflicting data stories. Fusedash allows organizations to define core company KPIs once and then deploy them across customized dashboards for sales, finance, support, and product teams. This ensures every department is measuring success with the same definitions, fostering alignment and collaborative problem-solving based on unified data.
Threat Watch
Proactive Risk Management
Organizations can leverage Threat Watch to adopt a proactive risk management strategy, identifying and addressing vulnerabilities before they can be exploited by malicious actors. This reduces the likelihood of costly data breaches and enhances overall cybersecurity resilience.
Regulatory Compliance
Compliance officers can utilize Threat Watch to streamline their compliance efforts by continuously monitoring for security gaps and ensuring that all necessary measures are in place to meet regulatory requirements. This capability is essential for maintaining trust and avoiding penalties.
Incident Response Enhancement
In the event of a cyber incident, Threat Watch equips organizations with the threat intelligence needed to respond effectively. With real-time insights and automated assessments, security teams can react swiftly and decisively, mitigating damage and recover more efficiently.
Strategic Security Planning
Security leaders can use the insights provided by Threat Watch to inform their strategic planning. By understanding their security posture and the evolving threat landscape, organizations can allocate resources more effectively and develop long-term strategies to fortify their defenses.
Overview
About Fusedash
Fusedash is the definitive AI-powered data visualization platform engineered for modern teams who demand clarity, consistency, and decisive action from their data. It transcends the limitations of fragmented analytics tools by providing a singular, intelligent workspace where raw data from disparate sources is transformed into a coherent, decision-ready narrative. Designed for organizations weary of manual reporting cycles and conflicting data interpretations, Fusedash establishes a single source of truth. Its core genius lies in operationalizing consistency: key metrics and KPIs are defined once and then seamlessly reused across every dashboard, interactive chart, detailed map, and narrative report. This ensures that leadership, marketing, operations, and beyond are all aligned, viewing and acting upon the same trusted numbers. Beyond mere monitoring, Fusedash empowers deep understanding with intuitive drill-down capabilities and integrated AI features like natural language data chat. It is more than a dashboard tool; it is a comprehensive platform for data storytelling, real-time monitoring, and collaborative insight, turning complex information into a strategic asset that drives organizational alignment and informed action.
About Threat Watch
In an era characterized by ceaseless digital transformation and increasingly sophisticated threats, Threat Watch stands out as a premier cybersecurity intelligence platform. This innovative solution is meticulously designed to empower organizations by providing a comprehensive assessment of their cybersecurity health. Threat Watch seamlessly integrates fragmented data sources, transforming them into a coherent and actionable narrative regarding an organization’s security posture. It goes beyond conventional point-in-time evaluations, offering a continuous and holistic view of assets, vulnerabilities, and exposures across the clear, deep, and dark web. Tailored for security leaders, IT managers, and compliance officers, Threat Watch equips these professionals with the insights necessary to transition from a reactive defense approach to a proactive resilience strategy. By synthesizing extensive streams of threat intelligence into a prioritized and visually accessible dashboard, Threat Watch empowers organizations to swiftly identify critical risks, automate intricate assessments, and implement effective mitigations with remarkable speed and assurance, thereby bolstering their defenses against an ever-evolving landscape of cyber threats.
Frequently Asked Questions
Fusedash FAQ
What types of data sources can I connect to Fusedash?
Fusedash offers flexible data integration capabilities to suit various workflows. You can start by uploading CSV files directly into the platform for quick analysis. For live, updated data, you can connect to a wide range of sources via API connections. The platform is designed to allow you to combine these datasets into a single, coherent view for comprehensive reporting and analysis.
How does Fusedash ensure data consistency across reports?
Consistency is a foundational principle of Fusedash. The platform allows you to centrally define your key metrics, dimensions, and calculation logic. Once these "single sources of truth" are established, you can reuse them across every dashboard, chart, map, and report you create. This means that whether the CEO or a marketing manager is viewing the data, they are guaranteed to be looking at numbers calculated the same way, eliminating conflicts and building trust.
Can I use Fusedash for real-time data monitoring?
Absolutely. Fusedash is built for both reflective analysis and proactive monitoring. By connecting to live data sources via APIs, you can create real-time interfaces and dashboards that update automatically. This allows teams to monitor critical KPIs, track live campaign performance, or oversee operational metrics as they happen, enabling swift identification and response to trends or issues.
Is technical expertise required to use the AI Chat and Chart Generator?
Not at all. A core design goal of Fusedash is to make advanced data exploration accessible. The AI Chart Generator guides you through visualization choices based on your data. The Smart Data Chat feature is designed for natural language interaction—you can ask questions like "What were sales by region last quarter?" or "Show me a trend of website traffic," and the AI will help find the answers and suggest appropriate visuals, requiring no code or complex query writing.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including enterprises, small to medium businesses, and institutions that prioritize cybersecurity. Regardless of size or industry, any organization seeking to enhance its cyber resilience can benefit from Threat Watch's comprehensive features.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and sophisticated data-gathering techniques to continuously scan the dark web for compromised credentials, phishing attempts, and other threats. This proactive monitoring ensures that organizations are alerted to risks that could impact their security.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security infrastructures. It offers integration capabilities with various security tools and platforms, allowing organizations to enhance their cybersecurity posture without disrupting their current workflows.
Is there a trial version available for Threat Watch?
Threat Watch typically offers potential users the opportunity to explore its features through a free scan, allowing organizations to evaluate the platform's capabilities and understand their cybersecurity health before committing to a subscription.
Alternatives
Fusedash Alternatives
Fusedash is an AI-powered data visualization and business intelligence platform designed to transform raw data into a unified source of truth. It enables teams to create consistent, decision-ready dashboards and reports, ensuring organizational alignment and action from a single workspace. Users may explore alternatives for various reasons, including specific budgetary constraints, the need for specialized features beyond core visualization, or integration requirements with a particular technical stack. The search often stems from a desire to find a solution that aligns perfectly with a team's unique scale, workflow, and data maturity. When evaluating options, it is essential to consider not only the breadth of visualizations but also the underlying architecture for data consistency. Key differentiators often lie in the efficiency of maintaining metric definitions, the depth of real-time analysis, and the sophistication of tools that democratize data access across all team members, from analysts to executives.
Threat Watch Alternatives
In the rapidly evolving digital landscape, Threat Watch stands as a premier cybersecurity intelligence platform, meticulously crafted to provide organizations with an instantaneous and sophisticated evaluation of their security posture. As businesses increasingly confront the complexities of cyber threats, many users find themselves seeking alternatives to Threat Watch. This quest often stems from a variety of factors, including pricing considerations, the need for specific features, or compatibility with existing platforms. When contemplating an alternative, it is vital to prioritize features that align with your organization's unique cybersecurity needs. Look for solutions that offer comprehensive insights into vulnerabilities, real-time exposure detection, and automated assessments. A user-friendly interface and robust support services should also be essential criteria, ensuring that the chosen platform effectively enhances your overall security strategy.