Karolium vs Threat Watch
Side-by-side comparison to help you choose the right product.
Karolium is a zero-code platform enabling enterprises to effortlessly create and customize intelligent applications for.
Last updated: February 28, 2026
Threat Watch
Threat Watch swiftly assesses your cybersecurity health, revealing vulnerabilities in compromised devices and accounts.
Last updated: March 1, 2026
Visual Comparison
Karolium

Threat Watch
Feature Comparison
Karolium
Unified Zero-Code Platform
Karolium's foundation lies in its zero-code capability, enabling users to create and customize applications without the need for traditional programming. This empowers non-technical users to engage directly in the development process, enhancing productivity and accelerating time-to-market for new solutions.
Pre-Composed Modules
The platform offers a suite of ready-to-use, pre-composed modules that organizations can leverage to augment existing application ecosystems effortlessly. This composability allows for tailored workflows that align precisely with business needs, eliminating the need for extensive redevelopment.
AI-Driven Business Intelligence
Karolium provides built-in predictive and prescriptive analytics, enabling enterprises to make informed decisions backed by data. This feature allows organizations to foresee trends, optimize operations, and implement strategies that align with future market demands.
Continuous Access and Enhancements
Delivered as a managed PaaS-driven SaaS platform, Karolium ensures users have continuous access to the latest capabilities and regular updates. This commitment to evolution allows organizations to stay ahead of technological advancements and market shifts without incurring additional costs.
Threat Watch
Continuous Threat Monitoring
Threat Watch provides real-time monitoring of your digital assets, ensuring that you are always aware of potential threats and vulnerabilities. This continuous vigilance enables organizations to respond swiftly to emerging risks and enhance their overall security posture.
Dark Web Surveillance
With a dedicated focus on the dark web, Threat Watch continuously scans for compromised credentials, breached accounts, and phishing addresses. This proactive surveillance allows organizations to detect threats before they can be exploited, significantly reducing the risk of data breaches.
Comprehensive Vulnerability Assessment
The platform evaluates critical security categories, delivering a detailed analysis of your organization's vulnerabilities. This feature empowers IT managers and security leaders to prioritize remediation efforts based on the most pressing risks identified within their systems.
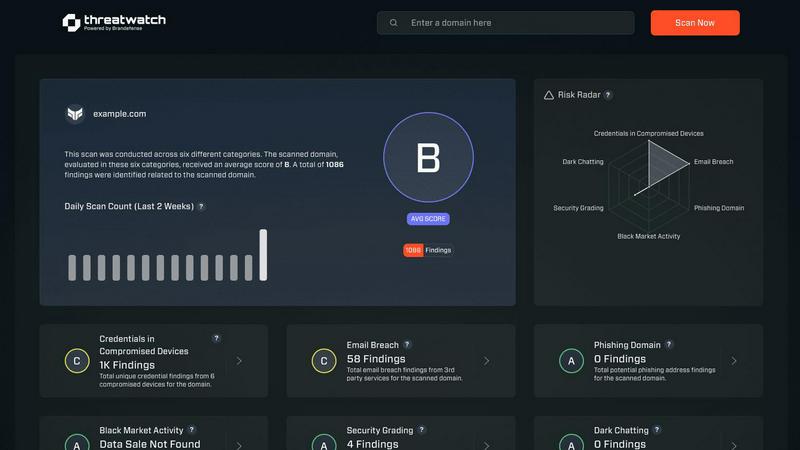
Intuitive Dashboard and Reporting
Threat Watch features an elegant, user-friendly dashboard that synthesizes vast amounts of threat intelligence into actionable insights. The intuitive interface allows users to quickly identify critical risks and generate reports that facilitate informed decision-making and strategic planning.
Use Cases
Karolium
Accelerating Digital Transformation
Organizations looking to rapidly build and deploy new applications can utilize Karolium to streamline their digital transformation efforts. By eliminating the complexities of traditional coding, businesses can focus on innovation and adaptability.
Enhancing Operational Agility
Karolium empowers enterprises to adapt swiftly to changing market conditions by providing a flexible platform that supports real-time collaboration and decision-making. This agility is crucial for maintaining competitiveness in today’s fast-paced business landscape.
Optimizing Supply Chain Management
With features designed for modern supply chain demands, Karolium enables businesses to improve supplier collaboration and centralize procurement processes. This results in enhanced efficiency, reduced costs, and improved supplier relationships across the board.
AI Integration for Intelligent Applications
Organizations eager to leverage AI across their operations can deploy Karolium to seamlessly integrate AI-driven solutions. From demand forecasting to asset monitoring, the platform facilitates the creation of intelligent applications that drive measurable business outcomes.
Threat Watch
Proactive Risk Management
Organizations can leverage Threat Watch to adopt a proactive risk management strategy, identifying and addressing vulnerabilities before they can be exploited by malicious actors. This reduces the likelihood of costly data breaches and enhances overall cybersecurity resilience.
Regulatory Compliance
Compliance officers can utilize Threat Watch to streamline their compliance efforts by continuously monitoring for security gaps and ensuring that all necessary measures are in place to meet regulatory requirements. This capability is essential for maintaining trust and avoiding penalties.
Incident Response Enhancement
In the event of a cyber incident, Threat Watch equips organizations with the threat intelligence needed to respond effectively. With real-time insights and automated assessments, security teams can react swiftly and decisively, mitigating damage and recover more efficiently.
Strategic Security Planning
Security leaders can use the insights provided by Threat Watch to inform their strategic planning. By understanding their security posture and the evolving threat landscape, organizations can allocate resources more effectively and develop long-term strategies to fortify their defenses.
Overview
About Karolium
Karolium represents a groundbreaking advancement in enterprise technology, functioning as a unified zero-code platform that empowers organizations to break free from the limitations of traditional software solutions. Designed for enterprises aiming to accelerate their digital transformation journey, Karolium enhances operational agility and enables businesses to leverage artificial intelligence without the complexities typically associated with custom coding. This sophisticated platform is tailored for organizations that seek to extract greater value from their existing application ecosystems, allowing for the rapid construction of bespoke solutions and seamless integration of predictive intelligence into core operations. By offering ready-to-deploy modules and a codeless customization environment, Karolium facilitates the swift development and enhancement of business applications, thus bridging the gap between legacy systems and modern microservices-ready applications. It is this holistic, intelligent platform that fosters seamless collaboration, proactive market navigation, and the strategic evolution of the enterprise as a whole.
About Threat Watch
In an era characterized by ceaseless digital transformation and increasingly sophisticated threats, Threat Watch stands out as a premier cybersecurity intelligence platform. This innovative solution is meticulously designed to empower organizations by providing a comprehensive assessment of their cybersecurity health. Threat Watch seamlessly integrates fragmented data sources, transforming them into a coherent and actionable narrative regarding an organization’s security posture. It goes beyond conventional point-in-time evaluations, offering a continuous and holistic view of assets, vulnerabilities, and exposures across the clear, deep, and dark web. Tailored for security leaders, IT managers, and compliance officers, Threat Watch equips these professionals with the insights necessary to transition from a reactive defense approach to a proactive resilience strategy. By synthesizing extensive streams of threat intelligence into a prioritized and visually accessible dashboard, Threat Watch empowers organizations to swiftly identify critical risks, automate intricate assessments, and implement effective mitigations with remarkable speed and assurance, thereby bolstering their defenses against an ever-evolving landscape of cyber threats.
Frequently Asked Questions
Karolium FAQ
What types of businesses can benefit from Karolium?
Karolium is designed for enterprises across various sectors seeking to enhance their operational efficiency, accelerate digital transformation, and leverage AI without the need for extensive coding knowledge.
How does Karolium integrate with existing systems?
Karolium provides seamless integration capabilities that allow organizations to connect with both legacy systems and modern microservices applications, ensuring a smooth transition and enhanced functionality.
Is there support available for users of Karolium?
Yes, Karolium offers comprehensive support resources, including documentation, training materials, and customer service to assist users in maximizing the platform's capabilities.
How frequently are new features and modules released?
Karolium follows a quarterly release schedule, providing users with new modules and enhancements regularly. This ensures that businesses can continuously access the latest features and improvements without additional costs.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including enterprises, small to medium businesses, and institutions that prioritize cybersecurity. Regardless of size or industry, any organization seeking to enhance its cyber resilience can benefit from Threat Watch's comprehensive features.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and sophisticated data-gathering techniques to continuously scan the dark web for compromised credentials, phishing attempts, and other threats. This proactive monitoring ensures that organizations are alerted to risks that could impact their security.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security infrastructures. It offers integration capabilities with various security tools and platforms, allowing organizations to enhance their cybersecurity posture without disrupting their current workflows.
Is there a trial version available for Threat Watch?
Threat Watch typically offers potential users the opportunity to explore its features through a free scan, allowing organizations to evaluate the platform's capabilities and understand their cybersecurity health before committing to a subscription.
Alternatives
Karolium Alternatives
Karolium is an advanced zero-code platform designed to empower enterprises in crafting and customizing intelligent applications that drive digital transformation. As a unified solution, it enables organizations to overcome the constraints of traditional software development, facilitating rapid deployment and integration of tailored applications. Businesses often seek alternatives to Karolium for various reasons, including pricing considerations, specific feature sets, or unique platform requirements that may not align perfectly with their operational needs. When exploring alternatives, it is crucial to evaluate factors such as ease of use, scalability, integration capabilities, and the breadth of pre-composed modules offered. Additionally, potential users should consider the level of support and documentation available, ensuring that the chosen platform not only meets their current demands but also adapts to future challenges in a dynamic business environment.
Threat Watch Alternatives
In the rapidly evolving digital landscape, Threat Watch stands as a premier cybersecurity intelligence platform, meticulously crafted to provide organizations with an instantaneous and sophisticated evaluation of their security posture. As businesses increasingly confront the complexities of cyber threats, many users find themselves seeking alternatives to Threat Watch. This quest often stems from a variety of factors, including pricing considerations, the need for specific features, or compatibility with existing platforms. When contemplating an alternative, it is vital to prioritize features that align with your organization's unique cybersecurity needs. Look for solutions that offer comprehensive insights into vulnerabilities, real-time exposure detection, and automated assessments. A user-friendly interface and robust support services should also be essential criteria, ensuring that the chosen platform effectively enhances your overall security strategy.