iGPT vs Threat Watch
Side-by-side comparison to help you choose the right product.
iGPT provides secure, intelligent email context for enterprise AI agents and workflows.
Last updated: February 28, 2026
Threat Watch
Threat Watch swiftly assesses your cybersecurity health, revealing vulnerabilities in compromised devices and accounts.
Last updated: March 1, 2026
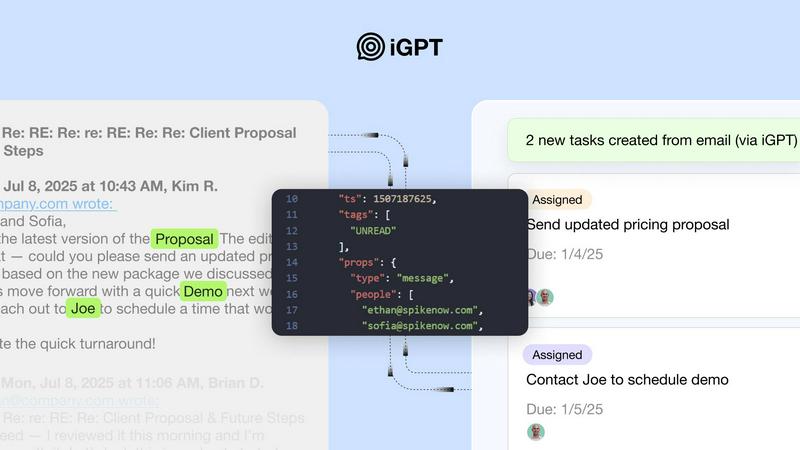
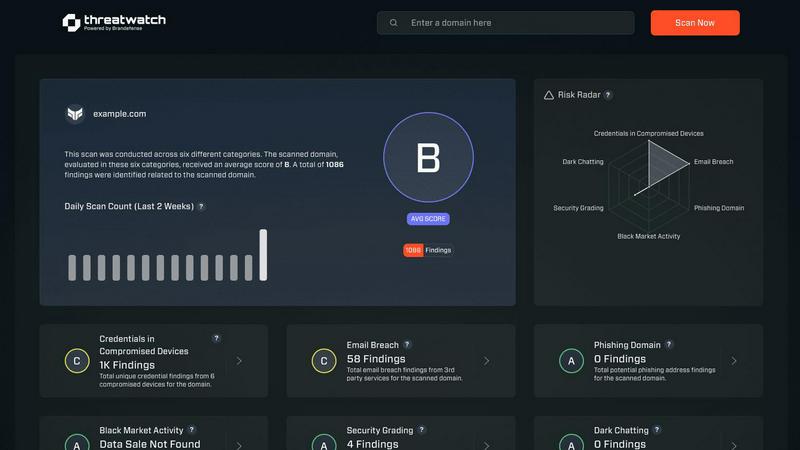
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Unified Intelligence Endpoint
iGPT consolidates the entire complexity of context engineering into a single, natural language API call. This unified endpoint seamlessly orchestrates real-time retrieval, sophisticated context shaping, and structured reasoning in one cohesive pipeline. Developers are liberated from the burden of managing multiple disparate services for parsing, vector stores, and prompt chains, enabling them to integrate powerful email intelligence with minimal code and operational overhead.
Autonomous Context Engineering
The platform autonomously handles the intricate tasks required to make email data usable for AI. This includes deep, automatic indexing of messages and attachments, intelligent reconstruction of email threads across time and participants, and optimized context window shaping for large language models. This sophisticated engineering happens behind the scenes, delivering clean, cited, and context-rich answers without any manual prompt tuning or maintenance from the user.
Enterprise-Grade Security Architecture
Security and data sovereignty are foundational to iGPT's design. It operates on a strict zero-data retention policy, processing each inference entirely in memory without storing inputs, prompts, or outputs. Coupled with OAuth-only authentication, rigorous Role-Based Access Control (RBAC), and comprehensive audit trails, it ensures that sensitive communication data never leaves a company's control and is never used to train external models.
Advanced Attachment & Thread Processing
iGPT excels at understanding the full context of communication by deeply processing not just email text, but all embedded attachments—including documents, PDFs, and spreadsheets—extracting their text, data, and structure. Furthermore, it intelligently reconstructs fragmented email threads, piecing together conversations across time and multiple participants to provide a complete and accurate narrative for the AI to reason over.
Threat Watch
Continuous Threat Monitoring
Threat Watch provides real-time monitoring of your digital assets, ensuring that you are always aware of potential threats and vulnerabilities. This continuous vigilance enables organizations to respond swiftly to emerging risks and enhance their overall security posture.
Dark Web Surveillance
With a dedicated focus on the dark web, Threat Watch continuously scans for compromised credentials, breached accounts, and phishing addresses. This proactive surveillance allows organizations to detect threats before they can be exploited, significantly reducing the risk of data breaches.
Comprehensive Vulnerability Assessment
The platform evaluates critical security categories, delivering a detailed analysis of your organization's vulnerabilities. This feature empowers IT managers and security leaders to prioritize remediation efforts based on the most pressing risks identified within their systems.
Intuitive Dashboard and Reporting
Threat Watch features an elegant, user-friendly dashboard that synthesizes vast amounts of threat intelligence into actionable insights. The intuitive interface allows users to quickly identify critical risks and generate reports that facilitate informed decision-making and strategic planning.
Use Cases
iGPT
Intelligent Email Assistants & Copilots
Build sophisticated AI agents that can draft, prioritize, summarize, and act on email with full situational awareness. These assistants understand the nuance of long threads, recognize urgency from tone, and can manage inboxes or draft contextually perfect responses by leveraging the entire history of a conversation and its related files.
Automated Workflow & Task Orchestration
Transform unstructured email exchanges into structured, actionable business processes. Automatically extract action items, deadlines, approvals, and decisions from board meetings or project updates, and convert them into tasks in tools like Jira or Asana. Proactively flag stalled conversations or follow-ups that require attention.
Customer Support & Relationship Intelligence
Empower support copilots and CRM agents with the complete customer story. iGPT can instantly rebuild a customer's journey from scattered email chains and attachments, allowing agents to understand past issues, commitments, and sentiment shifts. It can also extract deal momentum, ownership, and key decisions directly from sales threads.
Compliance, Audit, and Insight Generation
Create a verifiable audit trail of feedback, approvals, and operational rationale by tracing every AI-generated insight back to its source emails and attachments. Automatically summarize legal contracts, invoices, or reports within the context of the surrounding email discussion for faster review and insight discovery.
Threat Watch
Proactive Risk Management
Organizations can leverage Threat Watch to adopt a proactive risk management strategy, identifying and addressing vulnerabilities before they can be exploited by malicious actors. This reduces the likelihood of costly data breaches and enhances overall cybersecurity resilience.
Regulatory Compliance
Compliance officers can utilize Threat Watch to streamline their compliance efforts by continuously monitoring for security gaps and ensuring that all necessary measures are in place to meet regulatory requirements. This capability is essential for maintaining trust and avoiding penalties.
Incident Response Enhancement
In the event of a cyber incident, Threat Watch equips organizations with the threat intelligence needed to respond effectively. With real-time insights and automated assessments, security teams can react swiftly and decisively, mitigating damage and recover more efficiently.
Strategic Security Planning
Security leaders can use the insights provided by Threat Watch to inform their strategic planning. By understanding their security posture and the evolving threat landscape, organizations can allocate resources more effectively and develop long-term strategies to fortify their defenses.
Overview
About iGPT
iGPT represents the definitive intelligence layer for enterprise communication, engineered to unlock the operational knowledge trapped within email silos. In an age where email remains the central nervous system of business, conventional AI solutions often falter, unable to parse the nuanced, unstructured data of conversations, threads, and attachments. iGPT elegantly solves this by acting as a secure, unified API that transforms complex email data into trusted, context-aware insights ready for autonomous agents and sophisticated AI workflows. Designed for forward-thinking developers and enterprises, its core value proposition is singular: to eliminate the arduous, maintenance-heavy tasks of data parsing, chunking, indexing, and prompt tuning. Instead, it provides a single, intelligent endpoint that handles the entire spectrum of context engineering—from real-time ingestion and hybrid retrieval to intelligent thread reconstruction. This allows organizations to ship reliable, production-ready agents with unparalleled speed, focusing on creating value rather than managing infrastructure. With an unwavering commitment to enterprise-grade security through principles like zero-data retention and strict RBAC, iGPT empowers businesses to automate critical follow-ups, drive agentic workflows, and unlock decision intelligence with absolute confidence and compliance.
About Threat Watch
In an era characterized by ceaseless digital transformation and increasingly sophisticated threats, Threat Watch stands out as a premier cybersecurity intelligence platform. This innovative solution is meticulously designed to empower organizations by providing a comprehensive assessment of their cybersecurity health. Threat Watch seamlessly integrates fragmented data sources, transforming them into a coherent and actionable narrative regarding an organization’s security posture. It goes beyond conventional point-in-time evaluations, offering a continuous and holistic view of assets, vulnerabilities, and exposures across the clear, deep, and dark web. Tailored for security leaders, IT managers, and compliance officers, Threat Watch equips these professionals with the insights necessary to transition from a reactive defense approach to a proactive resilience strategy. By synthesizing extensive streams of threat intelligence into a prioritized and visually accessible dashboard, Threat Watch empowers organizations to swiftly identify critical risks, automate intricate assessments, and implement effective mitigations with remarkable speed and assurance, thereby bolstering their defenses against an ever-evolving landscape of cyber threats.
Frequently Asked Questions
iGPT FAQ
How does iGPT handle data privacy and security?
iGPT is built with enterprise-grade security as a core principle. It employs a zero-data retention model, meaning your data is processed in memory for the duration of an API call and is never written to disk or stored. Data is never used to train models. Access is strictly controlled via OAuth and RBAC, and every action is logged to a full audit trail, ensuring complete data sovereignty and compliance.
What is the "unified endpoint" and how does it simplify development?
The unified endpoint is a single API call (like /v1/recall/ask/) that replaces the need for a complex, multi-step retrieval-augmented generation (RAG) pipeline. Instead of developers managing separate services for ingestion, chunking, embedding, vector search, and prompt engineering, they simply send a natural language query. iGPT internally handles all those steps—retrieval, context shaping, and reasoning—returning a structured, cited answer.
Can iGPT process attachments within emails?
Yes, advanced attachment processing is a key capability. iGPT automatically extracts and indexes text, data, and structural information from a wide variety of file attachments, including PDFs, Word documents, spreadsheets, and presentations. This content is then made available for retrieval and reasoning in the context of the email thread, allowing questions about data within a report or terms in a contract to be answered accurately.
How quickly can I integrate and start using iGPT?
Integration is designed for immediacy. iGPT provides a live playground to test API requests with your own data, comprehensive SDKs, and detailed documentation. You can connect email sources, and the platform begins deep indexing automatically. This allows developers to go from sign-up to receiving contextual answers from their email data in a very short timeframe, accelerating prototyping and production deployment.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including enterprises, small to medium businesses, and institutions that prioritize cybersecurity. Regardless of size or industry, any organization seeking to enhance its cyber resilience can benefit from Threat Watch's comprehensive features.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and sophisticated data-gathering techniques to continuously scan the dark web for compromised credentials, phishing attempts, and other threats. This proactive monitoring ensures that organizations are alerted to risks that could impact their security.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security infrastructures. It offers integration capabilities with various security tools and platforms, allowing organizations to enhance their cybersecurity posture without disrupting their current workflows.
Is there a trial version available for Threat Watch?
Threat Watch typically offers potential users the opportunity to explore its features through a free scan, allowing organizations to evaluate the platform's capabilities and understand their cybersecurity health before committing to a subscription.
Alternatives
iGPT Alternatives
iGPT represents the pinnacle of enterprise-grade intelligence for communication data, a sophisticated layer engineered to transform unstructured email and messaging content into secure, actionable context for AI agents and workflows. As a definitive solution in business intelligence, it addresses the critical challenge of unlocking operational knowledge trapped within communication silos with unparalleled security and speed. Organizations may explore alternatives for various strategic reasons, including specific budget constraints, the need for different integration capabilities, or a preference for building bespoke internal systems. The landscape offers a spectrum of approaches, from foundational API toolkits to more specialized data processing platforms. When evaluating options, discerning enterprises should prioritize solutions that offer robust, auditable security protocols, genuine proficiency in handling the nuanced complexity of communication threads, and a clear path to reliable production deployment. The true measure lies in a platform's ability to deliver trusted, context-aware intelligence without imposing unsustainable maintenance burdens or compromising on data sovereignty.
Threat Watch Alternatives
In the rapidly evolving digital landscape, Threat Watch stands as a premier cybersecurity intelligence platform, meticulously crafted to provide organizations with an instantaneous and sophisticated evaluation of their security posture. As businesses increasingly confront the complexities of cyber threats, many users find themselves seeking alternatives to Threat Watch. This quest often stems from a variety of factors, including pricing considerations, the need for specific features, or compatibility with existing platforms. When contemplating an alternative, it is vital to prioritize features that align with your organization's unique cybersecurity needs. Look for solutions that offer comprehensive insights into vulnerabilities, real-time exposure detection, and automated assessments. A user-friendly interface and robust support services should also be essential criteria, ensuring that the chosen platform effectively enhances your overall security strategy.