CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right product.
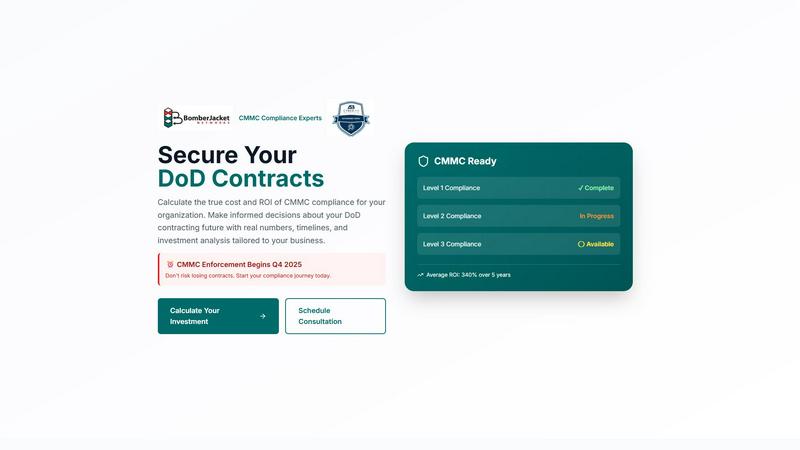
CMMC ROI
Calculate your precise CMMC compliance investment and potential return to secure DoD contracts.
Last updated: March 1, 2026
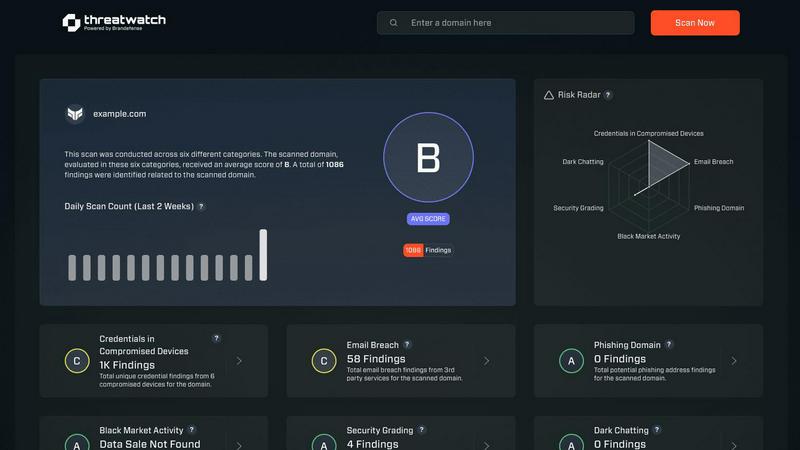
Threat Watch
Threat Watch swiftly assesses your cybersecurity health, revealing vulnerabilities in compromised devices and accounts.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Personalized Investment Calculator
The platform's core is a dynamic, personalized calculator that allows organizations to input their specific company size, DoD revenue, required CMMC level, and current compliance status. It then generates a detailed, multi-year financial projection, offering a clear range of total investment costs and a precise calculation of the expected ROI, transforming abstract requirements into concrete financial data.
Executive-Level ROI & Payback Analysis
CMMC ROI distills complex financial projections into clear, executive-friendly metrics. It provides a definitive Return on Investment percentage, a calculated payback period indicating the break-even point, and a visual timeline projection. These powerful outputs are designed to justify cybersecurity expenditures and secure crucial budget approvals from leadership and stakeholders.
Comprehensive Cost & Timeline Modeling
Beyond simple calculations, the platform offers a holistic view of the compliance journey. It models the full investment lifecycle, including initial implementation, annual maintenance costs, and future recertification expenses. Furthermore, it outlines a detailed 12-month implementation timeline, providing a realistic roadmap from gap assessment to final certification.
Comparative Scenario & Risk Assessment
Users can instantly load pre-configured scenarios for different contractor profiles to benchmark their situation or input custom data for a fully personalized analysis. The platform also includes a critical risk assessment module, quantifying the dire financial consequences of non-compliance, including 100% contract loss risk and average breach costs, thereby underscoring the investment's necessity.
Threat Watch
Continuous Threat Monitoring
Threat Watch provides real-time monitoring of your digital assets, ensuring that you are always aware of potential threats and vulnerabilities. This continuous vigilance enables organizations to respond swiftly to emerging risks and enhance their overall security posture.
Dark Web Surveillance
With a dedicated focus on the dark web, Threat Watch continuously scans for compromised credentials, breached accounts, and phishing addresses. This proactive surveillance allows organizations to detect threats before they can be exploited, significantly reducing the risk of data breaches.
Comprehensive Vulnerability Assessment
The platform evaluates critical security categories, delivering a detailed analysis of your organization's vulnerabilities. This feature empowers IT managers and security leaders to prioritize remediation efforts based on the most pressing risks identified within their systems.
Intuitive Dashboard and Reporting
Threat Watch features an elegant, user-friendly dashboard that synthesizes vast amounts of threat intelligence into actionable insights. The intuitive interface allows users to quickly identify critical risks and generate reports that facilitate informed decision-making and strategic planning.
Use Cases
CMMC ROI
Securing Executive Buy-In & Budget Approval
CFOs, CEOs, and board members utilize the platform's precise ROI calculations and payback timelines to build a compelling, data-driven business case for CMMC compliance investments. The generated executive briefing provides the financial justification needed to allocate significant capital and resources toward achieving certification.
Strategic Planning for Small & Medium Businesses
Small and medium-sized defense contractors with limited resources use CMMC ROI to understand the full financial scope of compliance. It helps them plan strategically, budget accurately over multiple years, and make informed decisions about pursuing DoD contracts that require specific CMMC levels, ensuring their business model remains viable.
Vendor & Supply Chain Compliance Justification
Prime contractors and larger organizations can use the platform to model the financial imperative for their subcontractors and supply chain partners to achieve compliance. The clear ROI analysis facilitates conversations and provides a tool for partners to understand their own investment, strengthening the entire supply chain's security posture.
Investment Prioritization & Roadmap Development
Compliance and IT directors leverage the detailed cost breakdown and timeline features to prioritize initiatives, sequence projects, and develop a phased implementation roadmap. This allows for efficient resource allocation, managing internal expectations, and tracking progress against a clear financial and temporal model.
Threat Watch
Proactive Risk Management
Organizations can leverage Threat Watch to adopt a proactive risk management strategy, identifying and addressing vulnerabilities before they can be exploited by malicious actors. This reduces the likelihood of costly data breaches and enhances overall cybersecurity resilience.
Regulatory Compliance
Compliance officers can utilize Threat Watch to streamline their compliance efforts by continuously monitoring for security gaps and ensuring that all necessary measures are in place to meet regulatory requirements. This capability is essential for maintaining trust and avoiding penalties.
Incident Response Enhancement
In the event of a cyber incident, Threat Watch equips organizations with the threat intelligence needed to respond effectively. With real-time insights and automated assessments, security teams can react swiftly and decisively, mitigating damage and recover more efficiently.
Strategic Security Planning
Security leaders can use the insights provided by Threat Watch to inform their strategic planning. By understanding their security posture and the evolving threat landscape, organizations can allocate resources more effectively and develop long-term strategies to fortify their defenses.
Overview
About CMMC ROI
CMMC ROI is an indispensable, data-driven investment analysis platform meticulously crafted for the Defense Industrial Base. It elegantly reframes the impending Cybersecurity Maturity Model Certification (CMMC) mandate from a nebulous compliance burden into a lucid, quantifiable strategic investment. As the enforcement deadline of Q4 2025 approaches, the platform serves as a critical financial compass for DoD contractors of all sizes—from emerging small businesses to established prime contractors. It empowers executives and financial leaders to transcend guesswork by generating a bespoke, multi-year financial model that projects the full spectrum of compliance costs, including implementation, ongoing maintenance, and triennial recertification. This comprehensive cost analysis is then juxtaposed against the tangible value of securing existing contract revenue, enhancing competitive win rates, and averting catastrophic breach-related losses. By delivering precise, boardroom-ready metrics such as Return on Investment percentage and payback period, CMMC ROI provides the financial clarity and justification needed to secure budget approvals and navigate the compliance journey with unwavering confidence and strategic foresight.
About Threat Watch
In an era characterized by ceaseless digital transformation and increasingly sophisticated threats, Threat Watch stands out as a premier cybersecurity intelligence platform. This innovative solution is meticulously designed to empower organizations by providing a comprehensive assessment of their cybersecurity health. Threat Watch seamlessly integrates fragmented data sources, transforming them into a coherent and actionable narrative regarding an organization’s security posture. It goes beyond conventional point-in-time evaluations, offering a continuous and holistic view of assets, vulnerabilities, and exposures across the clear, deep, and dark web. Tailored for security leaders, IT managers, and compliance officers, Threat Watch equips these professionals with the insights necessary to transition from a reactive defense approach to a proactive resilience strategy. By synthesizing extensive streams of threat intelligence into a prioritized and visually accessible dashboard, Threat Watch empowers organizations to swiftly identify critical risks, automate intricate assessments, and implement effective mitigations with remarkable speed and assurance, thereby bolstering their defenses against an ever-evolving landscape of cyber threats.
Frequently Asked Questions
CMMC ROI FAQ
How does CMMC ROI calculate the Return on Investment?
The platform uses a sophisticated formula: ROI = (Protected Value - Total Investment) / Total Investment × 100. Protected Value includes your five-year DoD contract revenue at risk plus an average breach cost avoidance of $2.5M. The Total Investment sums your implementation costs, five years of maintenance, and one recertification event, providing a comprehensive financial picture.
What if my company is already working on CMMC compliance?
The calculator accounts for your progress. You can select "In Progress" or "Nearly Complete" as your current status, which applies a significant discount (30% or 60%, respectively) to the implementation cost estimate. This ensures your personalized ROI reflects the investment you have already made, giving you credit for work completed.
Are the cost estimates provided by CMMC ROI accurate?
The platform provides data-driven cost ranges based on company size and CMMC level, developed by CMMC compliance experts. While it offers a highly reliable projection for planning and justification, the final investment can vary based on your specific environment, existing infrastructure, and chosen implementation partners. It is designed as a precise planning tool.
What happens if I don't pursue CMMC certification?
The risk assessment module clearly quantifies the consequence: a 100% risk to your existing DoD contract revenue once enforcement begins. Furthermore, you forgo the competitive advantage in new bids and remain exposed to significant breach and false claims costs, which the platform estimates at an average of $2.5M, making non-compliance a far costlier path.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including enterprises, small to medium businesses, and institutions that prioritize cybersecurity. Regardless of size or industry, any organization seeking to enhance its cyber resilience can benefit from Threat Watch's comprehensive features.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and sophisticated data-gathering techniques to continuously scan the dark web for compromised credentials, phishing attempts, and other threats. This proactive monitoring ensures that organizations are alerted to risks that could impact their security.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security infrastructures. It offers integration capabilities with various security tools and platforms, allowing organizations to enhance their cybersecurity posture without disrupting their current workflows.
Is there a trial version available for Threat Watch?
Threat Watch typically offers potential users the opportunity to explore its features through a free scan, allowing organizations to evaluate the platform's capabilities and understand their cybersecurity health before committing to a subscription.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a sophisticated business intelligence platform designed to transform the complex financial planning of Cybersecurity Maturity Model Certification compliance into a clear, quantifiable strategic investment. It provides defense contractors with a precise, data-driven analysis of costs, return, and payback timelines, enabling confident budget and strategic decisions ahead of the 2025 mandate enforcement. Organizations may explore alternatives for various reasons, including specific budgetary constraints, a need for different feature integrations, or a preference for a different analytical methodology. The search for a different solution is a natural part of due diligence in selecting a strategic planning tool. When evaluating any platform, discerning leaders should prioritize solutions that offer not just cost estimation, but true investment intelligence. The ideal tool delivers personalized, multi-year financial modeling, a clear calculation of return on investment and payback period, and the sophisticated analytics necessary to justify cybersecurity expenditures as a core business imperative.
Threat Watch Alternatives
In the rapidly evolving digital landscape, Threat Watch stands as a premier cybersecurity intelligence platform, meticulously crafted to provide organizations with an instantaneous and sophisticated evaluation of their security posture. As businesses increasingly confront the complexities of cyber threats, many users find themselves seeking alternatives to Threat Watch. This quest often stems from a variety of factors, including pricing considerations, the need for specific features, or compatibility with existing platforms. When contemplating an alternative, it is vital to prioritize features that align with your organization's unique cybersecurity needs. Look for solutions that offer comprehensive insights into vulnerabilities, real-time exposure detection, and automated assessments. A user-friendly interface and robust support services should also be essential criteria, ensuring that the chosen platform effectively enhances your overall security strategy.
