Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right product.
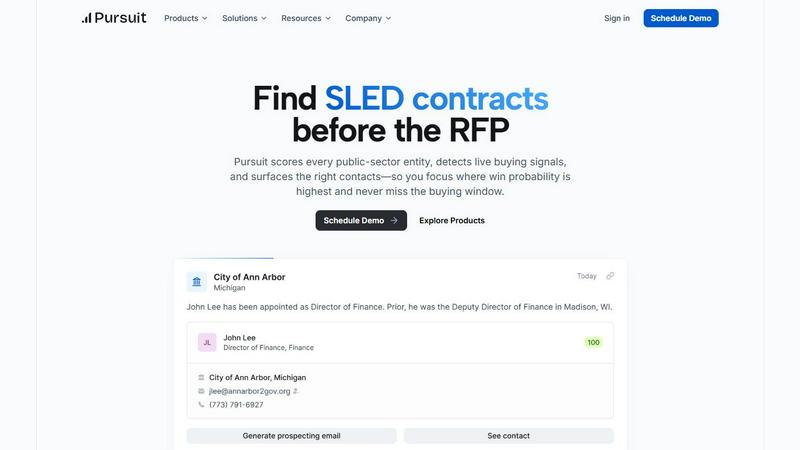
Pursuit
Pursuit uncovers high-probability public sector contracts and essential contacts, empowering your team to win before.
Last updated: February 28, 2026
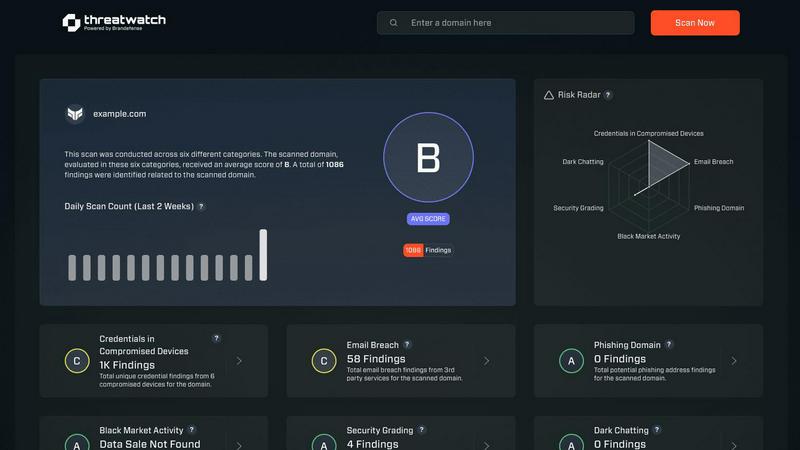
Threat Watch
Threat Watch swiftly assesses your cybersecurity health, revealing vulnerabilities in compromised devices and accounts.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Proactive Buying Signal Detection
Pursuit excels in surfacing buying signals 6 to 18 months prior to RFP releases. This foresight enables sales teams to position themselves as incumbents rather than outsiders, fostering stronger relationships and trust with potential clients.
Comprehensive Entity Research
With access to extensive data on over 110,000 public entities, Pursuit provides users with a clear understanding of unique procurement processes and timing, allowing businesses to tailor their strategies effectively and efficiently.
Integrated CRM Functionality
Pursuit offers seamless integration with popular CRM platforms such as Salesforce and HubSpot. This feature ensures that data flows automatically, enhancing operational efficiency and data accuracy across sales, marketing, and revenue teams.
Targeted Outreach Tools
The platform empowers teams by generating prioritized outreach lists based on real-time buying signals. This feature eliminates guesswork, allowing team members to focus on high-value prospects and increasing their chances of conversion.
Threat Watch
Continuous Threat Monitoring
Threat Watch provides real-time monitoring of your digital assets, ensuring that you are always aware of potential threats and vulnerabilities. This continuous vigilance enables organizations to respond swiftly to emerging risks and enhance their overall security posture.
Dark Web Surveillance
With a dedicated focus on the dark web, Threat Watch continuously scans for compromised credentials, breached accounts, and phishing addresses. This proactive surveillance allows organizations to detect threats before they can be exploited, significantly reducing the risk of data breaches.
Comprehensive Vulnerability Assessment
The platform evaluates critical security categories, delivering a detailed analysis of your organization's vulnerabilities. This feature empowers IT managers and security leaders to prioritize remediation efforts based on the most pressing risks identified within their systems.
Intuitive Dashboard and Reporting
Threat Watch features an elegant, user-friendly dashboard that synthesizes vast amounts of threat intelligence into actionable insights. The intuitive interface allows users to quickly identify critical risks and generate reports that facilitate informed decision-making and strategic planning.
Use Cases
Pursuit
Strategic Opportunity Identification
Sales teams can leverage Pursuit to identify high-probability opportunities well before RFPs are released. This proactive approach allows businesses to strategize effectively and engage with potential clients early on.
Enhanced Account-Based Marketing
Marketing teams can utilize Pursuit's insights to develop targeted account-based marketing campaigns. By aligning campaigns with real buying signals, they can improve their engagement and conversion rates significantly.
Efficient Sales Preparation
Account Executives can access vital information about potential clients instantly through Pursuit's Chrome extension. This feature equips them with insights on incumbents, contract values, and recent signals, enhancing their meeting preparedness.
Streamlined Customer Success Monitoring
Customer success teams benefit from Pursuit by receiving alerts for contract renewals and potential churn signals. This proactive monitoring allows them to address issues before they escalate, ensuring stronger client relationships.
Threat Watch
Proactive Risk Management
Organizations can leverage Threat Watch to adopt a proactive risk management strategy, identifying and addressing vulnerabilities before they can be exploited by malicious actors. This reduces the likelihood of costly data breaches and enhances overall cybersecurity resilience.
Regulatory Compliance
Compliance officers can utilize Threat Watch to streamline their compliance efforts by continuously monitoring for security gaps and ensuring that all necessary measures are in place to meet regulatory requirements. This capability is essential for maintaining trust and avoiding penalties.
Incident Response Enhancement
In the event of a cyber incident, Threat Watch equips organizations with the threat intelligence needed to respond effectively. With real-time insights and automated assessments, security teams can react swiftly and decisively, mitigating damage and recover more efficiently.
Strategic Security Planning
Security leaders can use the insights provided by Threat Watch to inform their strategic planning. By understanding their security posture and the evolving threat landscape, organizations can allocate resources more effectively and develop long-term strategies to fortify their defenses.
Overview
About Pursuit
Pursuit is an innovative AI-driven intelligence platform meticulously crafted for businesses that engage with the public sector, particularly in the realms of state, local, and education (SLED) procurement. By transforming a traditionally opaque landscape into an insightful and actionable strategic roadmap, Pursuit empowers sales, business development, and marketing teams within government technology vendors and contractors. The platform's core value lies in its ability to illuminate high-probability opportunities through precise entity scoring, detect real-time buying signals before formal RFPs are published, and identify key, verified contacts essential for assembling a winning buying committee. With comprehensive enterprise-level research on over 90,000 public entities and four million contacts, Pursuit enables teams to focus their efforts where they are most impactful, significantly enhancing pipeline generation and win rates, while ensuring that no critical buying window is overlooked.
About Threat Watch
In an era characterized by ceaseless digital transformation and increasingly sophisticated threats, Threat Watch stands out as a premier cybersecurity intelligence platform. This innovative solution is meticulously designed to empower organizations by providing a comprehensive assessment of their cybersecurity health. Threat Watch seamlessly integrates fragmented data sources, transforming them into a coherent and actionable narrative regarding an organization’s security posture. It goes beyond conventional point-in-time evaluations, offering a continuous and holistic view of assets, vulnerabilities, and exposures across the clear, deep, and dark web. Tailored for security leaders, IT managers, and compliance officers, Threat Watch equips these professionals with the insights necessary to transition from a reactive defense approach to a proactive resilience strategy. By synthesizing extensive streams of threat intelligence into a prioritized and visually accessible dashboard, Threat Watch empowers organizations to swiftly identify critical risks, automate intricate assessments, and implement effective mitigations with remarkable speed and assurance, thereby bolstering their defenses against an ever-evolving landscape of cyber threats.
Frequently Asked Questions
Pursuit FAQ
What types of businesses can benefit from Pursuit?
Pursuit is designed for businesses that engage with the public sector, particularly those involved in selling technology solutions to state, local, and education entities.
How does Pursuit detect buying signals?
The platform uses advanced AI algorithms to analyze various data sources, including council meetings and budget documents, to identify buying signals well before formal RFP announcements.
Can Pursuit integrate with existing CRM systems?
Yes, Pursuit offers native integrations with major CRM platforms like Salesforce and HubSpot, ensuring seamless data flow and enhanced operational efficiency for users.
What is the expected ROI from using Pursuit?
Many users have reported significant increases in their qualified pipeline, with some achieving up to 6.6 times their pipeline growth without adding new hires, demonstrating the platform's effectiveness in driving business success.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including enterprises, small to medium businesses, and institutions that prioritize cybersecurity. Regardless of size or industry, any organization seeking to enhance its cyber resilience can benefit from Threat Watch's comprehensive features.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and sophisticated data-gathering techniques to continuously scan the dark web for compromised credentials, phishing attempts, and other threats. This proactive monitoring ensures that organizations are alerted to risks that could impact their security.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security infrastructures. It offers integration capabilities with various security tools and platforms, allowing organizations to enhance their cybersecurity posture without disrupting their current workflows.
Is there a trial version available for Threat Watch?
Threat Watch typically offers potential users the opportunity to explore its features through a free scan, allowing organizations to evaluate the platform's capabilities and understand their cybersecurity health before committing to a subscription.
Alternatives
Pursuit Alternatives
Pursuit is an AI-driven intelligence platform designed to illuminate the complexities of public sector procurement for businesses targeting state, local, and education (SLED) sectors. By transforming opaque data into actionable insights, Pursuit provides a strategic advantage for sales, business development, and marketing teams within government technology vendors and contractors. Users often seek alternatives to Pursuit due to various factors, such as pricing considerations, specific feature sets, or unique platform requirements that better align with their operational needs. When exploring alternatives, it is essential to assess the breadth of data coverage, the sophistication of analytics provided, and the overall user experience to ensure that the chosen solution meets your strategic objectives and enhances your competitive edge.
Threat Watch Alternatives
In the rapidly evolving digital landscape, Threat Watch stands as a premier cybersecurity intelligence platform, meticulously crafted to provide organizations with an instantaneous and sophisticated evaluation of their security posture. As businesses increasingly confront the complexities of cyber threats, many users find themselves seeking alternatives to Threat Watch. This quest often stems from a variety of factors, including pricing considerations, the need for specific features, or compatibility with existing platforms. When contemplating an alternative, it is vital to prioritize features that align with your organization's unique cybersecurity needs. Look for solutions that offer comprehensive insights into vulnerabilities, real-time exposure detection, and automated assessments. A user-friendly interface and robust support services should also be essential criteria, ensuring that the chosen platform effectively enhances your overall security strategy.
