Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right product.

Deeploy
Deeploy empowers organizations to govern AI with confidence, ensuring risk management and compliance at scale.
Last updated: March 1, 2026
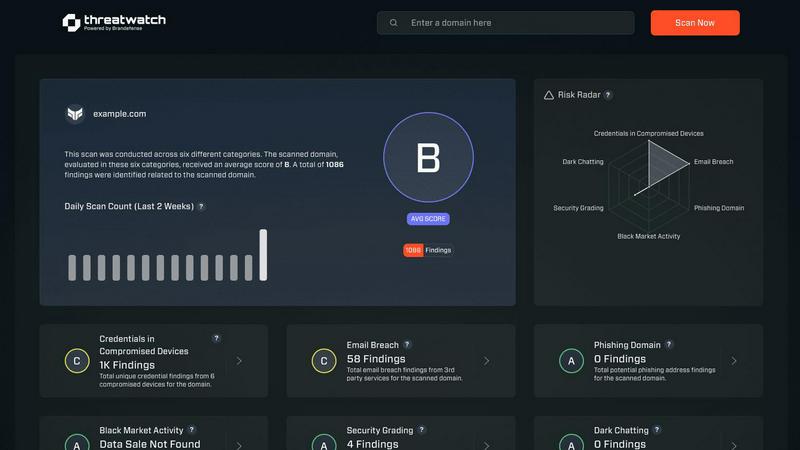
Threat Watch
Threat Watch swiftly assesses your cybersecurity health, revealing vulnerabilities in compromised devices and accounts.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
Deeploy offers a sophisticated interface for complete visibility across your AI landscape. This feature enables organizations to discover, onboard, and manage every AI system from a singular platform, effectively eliminating blind spots and ensuring centralized control without the burden of migration challenges.
Control Frameworks
Stay compliant with ease using guided workflows tailored to navigate the complexities of AI regulations. Deeploy allows users to select default control frameworks such as ISO 42001 and NIST AI RMF, or customize their own, enabling rapid classification of AI system risks and establishing accountability through streamlined approval processes.
Control Implementation
Transform governance frameworks into actionable controls that engineers can easily follow. Deeploy automates the assignment of clear, actionable requirements for every AI system, significantly accelerating compliance efforts by up to 90% through templates and auto-collected evidence, minimizing manual workload.
Real-Time Monitoring
Deeploy equips organizations with the ability to monitor AI performance in real-time, proactively detecting issues before they affect users or pose compliance risks. Instant alerts for model drift, performance drops, and the identification of errors ensure organizations maintain high operational standards while protecting user experience.
Threat Watch
Continuous Threat Monitoring
Threat Watch provides real-time monitoring of your digital assets, ensuring that you are always aware of potential threats and vulnerabilities. This continuous vigilance enables organizations to respond swiftly to emerging risks and enhance their overall security posture.
Dark Web Surveillance
With a dedicated focus on the dark web, Threat Watch continuously scans for compromised credentials, breached accounts, and phishing addresses. This proactive surveillance allows organizations to detect threats before they can be exploited, significantly reducing the risk of data breaches.
Comprehensive Vulnerability Assessment
The platform evaluates critical security categories, delivering a detailed analysis of your organization's vulnerabilities. This feature empowers IT managers and security leaders to prioritize remediation efforts based on the most pressing risks identified within their systems.
Intuitive Dashboard and Reporting
Threat Watch features an elegant, user-friendly dashboard that synthesizes vast amounts of threat intelligence into actionable insights. The intuitive interface allows users to quickly identify critical risks and generate reports that facilitate informed decision-making and strategic planning.
Use Cases
Deeploy
Regulatory Compliance
Organizations across various sectors utilize Deeploy to ensure adherence to stringent regulatory standards. By employing its guided workflows and control frameworks, compliance officers can swiftly navigate the complexities of regulations like the EU AI Act, ensuring that all AI initiatives are compliant from the outset.
AI Performance Management
Deeploy's real-time monitoring capabilities allow businesses to oversee AI system performance continuously. This ensures that any anomalies or performance drops are identified and addressed promptly, safeguarding user experience and operational integrity.
Centralized AI Oversight
Companies can consolidate their AI governance efforts by using Deeploy to create a central registry for all AI systems. This centralized approach simplifies oversight, making it easier for organizations to manage and audit their AI initiatives effectively.
Risk Mitigation
Deeploy empowers organizations to systematically identify and mitigate risks associated with AI deployment. By establishing clear accountability and automated evidence collection, it supports proactive risk management and enhances stakeholder trust.
Threat Watch
Proactive Risk Management
Organizations can leverage Threat Watch to adopt a proactive risk management strategy, identifying and addressing vulnerabilities before they can be exploited by malicious actors. This reduces the likelihood of costly data breaches and enhances overall cybersecurity resilience.
Regulatory Compliance
Compliance officers can utilize Threat Watch to streamline their compliance efforts by continuously monitoring for security gaps and ensuring that all necessary measures are in place to meet regulatory requirements. This capability is essential for maintaining trust and avoiding penalties.
Incident Response Enhancement
In the event of a cyber incident, Threat Watch equips organizations with the threat intelligence needed to respond effectively. With real-time insights and automated assessments, security teams can react swiftly and decisively, mitigating damage and recover more efficiently.
Strategic Security Planning
Security leaders can use the insights provided by Threat Watch to inform their strategic planning. By understanding their security posture and the evolving threat landscape, organizations can allocate resources more effectively and develop long-term strategies to fortify their defenses.
Overview
About Deeploy
Deeploy stands at the forefront of AI governance, providing a comprehensive platform meticulously designed for organizations that harness artificial intelligence at scale. In an era where AI's potential is both revolutionary and fraught with risk, Deeploy transforms this high-stakes landscape into a controlled, strategic asset. The platform centralizes oversight, compliance, and monitoring across every AI system within an enterprise—whether developed in-house, sourced from third-party vendors, or integrated into existing applications. Tailored for compliance officers, risk managers, and engineering leaders, Deeploy seamlessly bridges the gap between rigorous regulatory frameworks, such as the EU AI Act, ISO 42001, and NIST AI RMF, and actionable operational execution. Its primary value proposition lies in delivering complete visibility and enforceable control, empowering organizations to accelerate AI innovation with confidence while systematically mitigating risks, ensuring transparency, and fostering trust among stakeholders. By streamlining governance, Deeploy supports organizations in navigating the complexities of AI deployment, making it an essential ally in the journey toward responsible and effective AI utilization.
About Threat Watch
In an era characterized by ceaseless digital transformation and increasingly sophisticated threats, Threat Watch stands out as a premier cybersecurity intelligence platform. This innovative solution is meticulously designed to empower organizations by providing a comprehensive assessment of their cybersecurity health. Threat Watch seamlessly integrates fragmented data sources, transforming them into a coherent and actionable narrative regarding an organization’s security posture. It goes beyond conventional point-in-time evaluations, offering a continuous and holistic view of assets, vulnerabilities, and exposures across the clear, deep, and dark web. Tailored for security leaders, IT managers, and compliance officers, Threat Watch equips these professionals with the insights necessary to transition from a reactive defense approach to a proactive resilience strategy. By synthesizing extensive streams of threat intelligence into a prioritized and visually accessible dashboard, Threat Watch empowers organizations to swiftly identify critical risks, automate intricate assessments, and implement effective mitigations with remarkable speed and assurance, thereby bolstering their defenses against an ever-evolving landscape of cyber threats.
Frequently Asked Questions
Deeploy FAQ
How does Deeploy ensure compliance with AI regulations?
Deeploy provides guided workflows that simplify the navigation of complex AI regulations. Users can choose from default control frameworks or customize their own to ensure compliance is both straightforward and effective.
What types of AI systems can Deeploy manage?
Deeploy is versatile and can manage AI systems developed in-house, sourced from vendors, or integrated within existing applications. This flexibility allows organizations to maintain oversight across diverse AI landscapes.
Can Deeploy integrate with existing MLOps platforms?
Yes, Deeploy is designed to connect seamlessly with any MLOps or GenAI platform, facilitating a smooth onboarding process and eliminating potential blind spots in AI management.
What benefits does real-time monitoring provide?
Real-time monitoring ensures that organizations can detect issues such as model drift or performance drops before they impact users. This proactive approach enhances operational stability and compliance, fostering trust with stakeholders.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for a wide range of organizations, including enterprises, small to medium businesses, and institutions that prioritize cybersecurity. Regardless of size or industry, any organization seeking to enhance its cyber resilience can benefit from Threat Watch's comprehensive features.
How does Threat Watch monitor the dark web?
Threat Watch employs advanced algorithms and sophisticated data-gathering techniques to continuously scan the dark web for compromised credentials, phishing attempts, and other threats. This proactive monitoring ensures that organizations are alerted to risks that could impact their security.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to complement existing security infrastructures. It offers integration capabilities with various security tools and platforms, allowing organizations to enhance their cybersecurity posture without disrupting their current workflows.
Is there a trial version available for Threat Watch?
Threat Watch typically offers potential users the opportunity to explore its features through a free scan, allowing organizations to evaluate the platform's capabilities and understand their cybersecurity health before committing to a subscription.
Alternatives
Deeploy Alternatives
Deeploy is a sophisticated AI governance platform designed for organizations engaging with artificial intelligence at scale. It occupies a critical niche within the realm of business intelligence, providing the necessary governance and oversight to transform disparate AI initiatives into cohesive, compliant, and strategically managed assets. Users often seek alternatives to Deeploy due to various factors, including pricing structures, feature sets, and specific platform requirements that may better align with their operational needs. When evaluating alternatives, it is essential to consider aspects such as ease of integration, the robustness of compliance features, scalability, and the overall user experience to ensure that the chosen solution meets the unique demands of your organization.
Threat Watch Alternatives
In the rapidly evolving digital landscape, Threat Watch stands as a premier cybersecurity intelligence platform, meticulously crafted to provide organizations with an instantaneous and sophisticated evaluation of their security posture. As businesses increasingly confront the complexities of cyber threats, many users find themselves seeking alternatives to Threat Watch. This quest often stems from a variety of factors, including pricing considerations, the need for specific features, or compatibility with existing platforms. When contemplating an alternative, it is vital to prioritize features that align with your organization's unique cybersecurity needs. Look for solutions that offer comprehensive insights into vulnerabilities, real-time exposure detection, and automated assessments. A user-friendly interface and robust support services should also be essential criteria, ensuring that the chosen platform effectively enhances your overall security strategy.
