Alternatives to Threat Watch
Threat Watch swiftly assesses your cybersecurity health, revealing vulnerabilities in compromised devices and accounts.
16 alternatives found
Decker
Decker transforms consulting deliverables into a monetized OS, where AI workflows and expert networks replace scattered prompts with review-ready.

AI Business Name Generator
Craft distinctive, brandable business names instantly with our refined AI generator designed for discerning startups and enterprises.

MarketWrk
MarketWrk automates pricing intelligence and MAP monitoring to protect your brand's premium positioning.

Opal44
Opal44 transforms your website data into clear, actionable insights, making analytics accessible and easy to understand.

Fusedash
Fusedash transforms raw data into elegant, actionable dashboards and charts for instant team insights.
finban
finban empowers you to effortlessly manage liquidity, enabling confident decisions on hiring, taxes, and investments.

Zignt
Zignt streamlines contract management with reusable templates, instant signing, and automated reminders for effortless.

aVenture
aVenture provides comprehensive venture intelligence to analyze private companies and uncover emerging investment.

Karolium
Karolium is a zero-code platform enabling enterprises to effortlessly create and customize intelligent applications for.

Promotron
Promotron streamlines promotional sales with elegant cloud software, automating processes for distributors and.

Pursuit
Pursuit uncovers high-probability public sector contracts and essential contacts, empowering your team to win before.
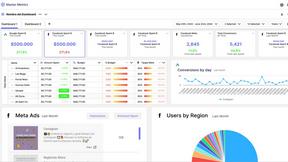
Master Metrics
Master Metrics elegantly transforms marketing data into actionable insights, empowering effortless, data-driven.

CMMC ROI
Calculate your precise CMMC compliance investment and potential return to secure DoD contracts.
Deeploy
Deeploy empowers organizations to govern AI with confidence, ensuring risk management and compliance at scale.
About Threat Watch Alternatives
In the rapidly evolving digital landscape, Threat Watch stands as a premier cybersecurity intelligence platform, meticulously crafted to provide organizations with an instantaneous and sophisticated evaluation of their security posture. As businesses increasingly confront the complexities of cyber threats, many users find themselves seeking alternatives to Threat Watch. This quest often stems from a variety of factors, including pricing considerations, the need for specific features, or compatibility with existing platforms. When contemplating an alternative, it is vital to prioritize features that align with your organization's unique cybersecurity needs. Look for solutions that offer comprehensive insights into vulnerabilities, real-time exposure detection, and automated assessments. A user-friendly interface and robust support services should also be essential criteria, ensuring that the chosen platform effectively enhances your overall security strategy.
FAQs about Threat Watch Alternatives
What is Threat Watch?
Threat Watch is a cybersecurity intelligence platform that provides a comprehensive and continuous evaluation of an organization's security posture.
Who is Threat Watch for?
Threat Watch is designed for security leaders, IT managers, and compliance officers who need to monitor and enhance their organization's cybersecurity resilience.
Is Threat Watch free?
Threat Watch is a premium service, and pricing details are typically provided upon inquiry.
What are the main features of Threat Watch?
The main features of Threat Watch include a comprehensive cyber health dashboard, real-time exposure detection, and automated asset and vulnerability assessment.